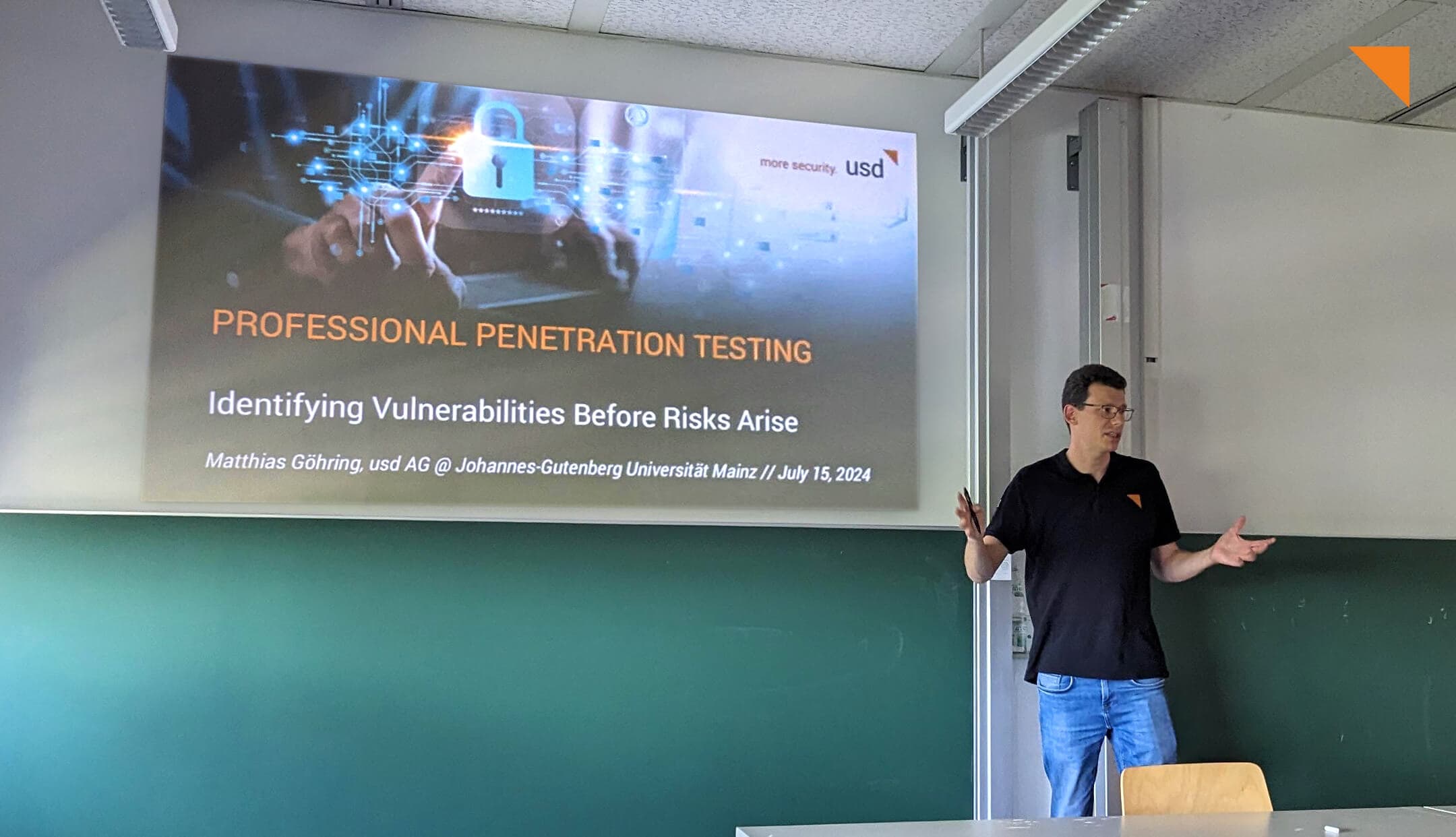
On July 15, 2024, Matthias Goehring, Head of usd HeroLab, was invited once again to give a guest lecture for the “IT Security” class by Prof. Dr....
Pentests & Security Analyses
Top 3 Vulnerabilities in Web Applications
During their penetration tests (pentests), our security analysts at usd HeroLab repeatedly uncover vulnerabilities that pose significant...
Top 3 Vulnerabilities in SAP Pentests
During their penetration tests (pentests), our security analysts at usd HeroLab repeatedly uncover vulnerabilities that pose significant risks to...
Security Advisory on WeKan
The pentest professionals at usd HeroLab examined the open source application WeKan during their pentests. This application offers users a solution...
Top 3 Vulnerabilities in Fat Client Pentests
During their penetration tests (pentests), our security analysts at usd HeroLab repeatedly uncover vulnerabilities that pose significant risks to...
Security Advisory on Gambio
The pentest professionals at usd HeroLab examined the online shop software Gambio during their pentests. The software offers merchants various...
Hacker Contest Winter Semester 2023/2024: 29 Students. 14 Vulnerabilities. 1 CVE. Countless Practical Insights.
Practical knowledge is often neglected during studies - but not for students at TU Darmstadt. In the winter semester, Matthias Göhring, Tobias...
Connect and Go: The usd OrangeBox Makes Preparing for Remote Pentests Easy
A penetration test or pentest provides answers to the question of whether attackers can penetrate your IT infrastructure. There are two ways in...
Top 3 Vulnerabilities in Mobile App Pentests
During their penetration tests (pentests), our security analysts at usd HeroLab repeatedly uncover vulnerabilities that pose significant risks to...
The Surprising Complexity of Finding Known Vulnerabilities
IT security professionals need an efficient and reliable solution for identifying known vulnerabilities in a software product, given its name and...
Secure or Not Secure, That Is the Question: “Cyber Security Assessments in Practice” at TU Munich
What are the different types of cyber security assessments? Why do companies undergo such security assessments? And how exactly does it work? Nico...
Security Assessment at All Levels: Pentest and Cloud Security Audit at Deutsche Fiskal
The need for a pentest is often driven by compliance requirements. However, in many cases, a pentest alone is not enough to make a reliable...