On March 31, 2022, the Payment Card Industry Security Standards Council (PCI SSC) released version 4.0 of PCI DSS - the most comprehensive update to the standard since version 1.0. To help you make the transition, we take a closer look at the key new features PCI DSS v.4.0 brings. In the first part of this blog post series, we look at the new Customized Approach.
The release of PCI DSS v4.0 introduced a more flexible framework that allows two approaches to implementing and validating PCI DSS requirements: the traditional approach (Defined Approach) and the Customized Approach, which allows organizations to create and implement individual security measures. For companies that follow the traditional approach, nothing changes - they continue to meet PCI DSS requirements as explicitly stipulated in the standard. The Customized Approach, on the other hand, offers companies more flexibility in meeting PCI DSS requirements. This is to support and enable the development of customized controls that can address evolving threats and technologies.
.
Defined vs. Customized Approach
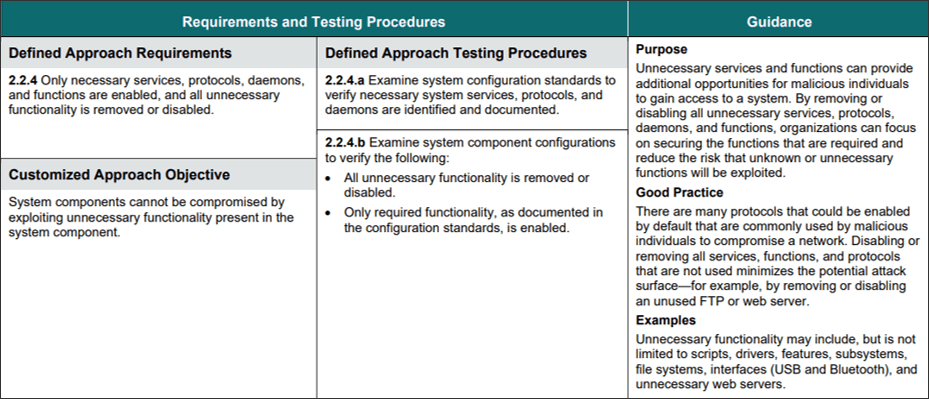
As before, the standard defines associated security measures (controls) for all requirements. Companies following the Defined Approach will achieve compliance as before by correctly implementing all specified measures. Most companies will likely continue to follow the traditional approach.
The Customized Approach now also enables companies to define and implement their own security measures for individual requirements. For this purpose, the standard specifies the control objective the individual measure must achieve.
Companies can therefore now decide whether to define their own controls for individual requirements. This is particularly interesting for companies that already have their own framework of security measures to satisfy different security standards at once.
Customized Approach
Companies that want to use the Customized Approach need to make some considerations. First, they need to fully understand the respective requirements. The PCI DSS v4.0 standard contains specific requirements for each requirement that must be implemented according to the Defined Approach and - listed separately - the security objective (Customized Approach Objective) of the requirement. This must be ensured by the measures according to the customized approach.
If the Customized Approach is chosen, companies can design and prepare measures to meet the security target of the corresponding requirement themselves. They must then submit these measures to their Qualified Security Assessors (QSAs) and have them assess whether the proposed measures meet the stated security objective. The assessor is responsible for deriving suitable test procedures that can be used in the course of the audit to verify whether the measures effectively meet the stated objective.
Criteria for Controls according to the Customized Approach
PCI DSS v4.0 formulates a number of criteria that a measure based on the Customized Approach must meet:
- PCI DSS 4.0 does not require an operational justification for the Customized Approach. The decision for this approach is up to the company.
- The requirements of PCI DSS can be met in a hybrid manner by applying both Defined Approach and Customized Approach measures simultaneously. This is even possible within a single requirement. The decisive factor is that the security objective of the requirement is met.
- The Customized Approach is not permitted for all requirements. Which requirements require the traditional approach is described in PCI DSS v4.0.
- The same measures can potentially be used to meet the security objectives of multiple requirements. Each requirement for which the Customized Approach is used must be validated individually by the assessor.
- Although it is possible in principle to satisfy many requirements using the Customized Approach, the complexity of an audit increases with the number of requirements using this approach. To simplify the audit, companies should try to keep the number of requirements using the Customized Approach as low as possible.
- Companies should always seek feedback from their assessor on Customized Approach measures. This should be done early, i.e. with sufficient lead time before the PCI DSS v4.0 audit.
- If possible, companies should design and implement their customized measures independently. QSAs are obliged to be independent of the company they audit. If the QSA is involved in the design, development, or implementation of a measure, a separate QSA will be required to test and evaluate it.
- Documentation is key to illustrating the effectiveness of individual measures. Organizations should collect and retain evidence that includes policies, procedures, system configuration settings, reports, logs, screenshots, etc. Policies, procedures, and other documentation should be aligned with and support the individual measures.
- A focused risk analysis is required for each individual action. This risk analysis outlines the harm the requirement is intended to prevent, describes the mismatch between defined requirement and aligned implementation, and explains how the individual action is intended to prevent harm. This targeted risk assessment is required and must be communicated to the assessor.
The Customized Approach is not permitted in a self-assessment using the Self-Assessment Questionnaire (SAQ). The measures specified in the standard must always be implemented there.
Outlook
With the introduction of the Customized Approach, PCI DSS v4.0 is well positioned to address current and future technology and security challenges. The increased flexibility of allowable security measures allows the standard to accommodate new and evolving technologies without having to lower its security requirements. Organizations that want to use the Customized Approach should take a close look at their environment and audit requirements and involve their assessor as early as possible in the planning process.



