How to prepare your company for the implementation of the Directive in good time
When it comes to implementing the NIS 2 Directive, our experts' clear recommendation to critical infrastructure operators is: Be the early bird - even if it seems difficult.
Get a head start by conducting a gap analysis in your company - regardless of whether you already have KRITIS audits carried out on the basis of the IT Security Act or are newly included in the scope of NIS-2. With the help of a gap analysis, you can uncover specific deviations between your company's security organization and the requirements of NIS 2. This allows you to plan and carry out suitable implementation projects in the coming year.
But let's take a step back first.
What is NIS 2?
The NIS 2 Directive (Network and Information Security 2, NIS 2) defines measures for a high common level of cyber security in the European Union. The aim is to ensure that organizations that are important for the smooth functioning of our society achieve a high level of digital security.
As a result, the requirements for operators of critical infrastructures (KRITIS) continue to grow. In Germany, the BSI Act obliges them to take appropriate organizational and technical precautions to protect their information technology systems, components and processes.
With the current IT Security Act 2.0, Germany was already a pioneer among EU member states since it had already implemented an extended scope and parts of the regulations now required in NIS 2. NIS 2 now extends the requirements for cybersecurity risk management and incident reporting obligations, for example, and includes additional sectors in its scope.
When does NIS 2 come into force?
As NIS 2 is an EU directive that must be transposed into national law by the individual member states, the member states are responsible for the specific formulation of the legal requirements and for monitoring compliance with them. It is to be expected that Germany will transpose the provisions of NIS 2 into an IT Security Act 3.0 and extend the existing Information Security Act. This transposition into national law must be completed by October 2024.
NIS 2 expands scope of application
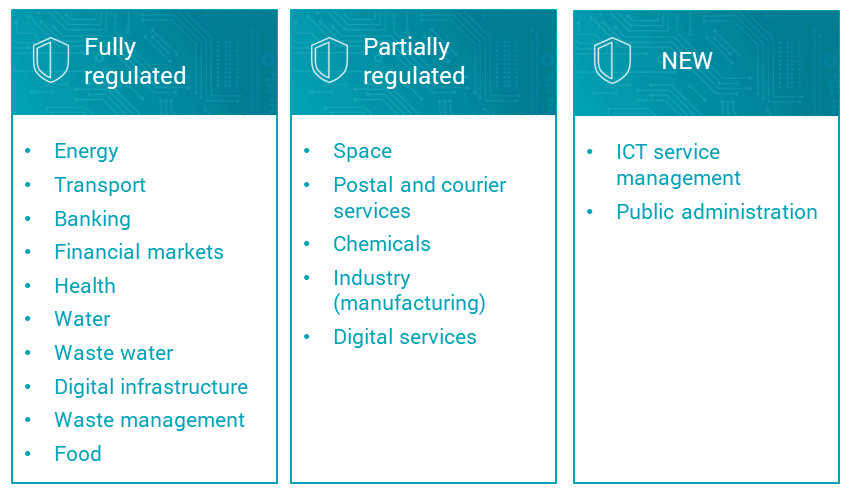
The scope of NIS 2 covers 18 sectors. A change in the threshold values will lead to an extension of the requirements to more organizations.
Some of these sectors are already fully or partially regulated by existing legislation in Germany, others are completely new:
We recommend that affected companies - especially in sectors that are only just coming into focus as a result of the NIS 2 Directive - take a look at the NIS 2 regulations at an early stage.
Gap analysis: Identify deviations & make preparations
As the transposition of NIS 2 into national law does not have to be completed until October 2024 and experience has shown that a transitional period will be granted, it may be tempting for many affected companies to wait and postpone preparations for the time being.
However, most of you are familiar with the extensive implementation projects for harmonization with regulatory requirements from other national industry or security standards. These are long-term projects that require extensive human and financial resources. These types of projects need ample preparation time and careful planning.
That’s why we recommend you make the most of the time you have left. Together with our experienced consultants and security auditors, review the requirements of NIS 2 now and identify deviations in your company. If specific requirements then follow with the publication of the IT Security Act, you will already have created a good basis - especially if your company has not yet been regulated by it.
Such a check has another advantage: While our auditors will focus on the requirements of NIS 2, the in-depth examination of your employees' processes, technology and security awareness will also give you a very good assessment of your company's security level.

Be the early bird in this case - for a head start in preparation and for more security. We are happy to help.



